Next-Generation
Cyber Security Platform
Unified visibility, proactive threat detection, and intelligent network protection
Our Security Solutions
Comprehensive protection across your entire security infrastructure
CAKRA
SIEM Platform - Centralized visibility and real-time security intelligence
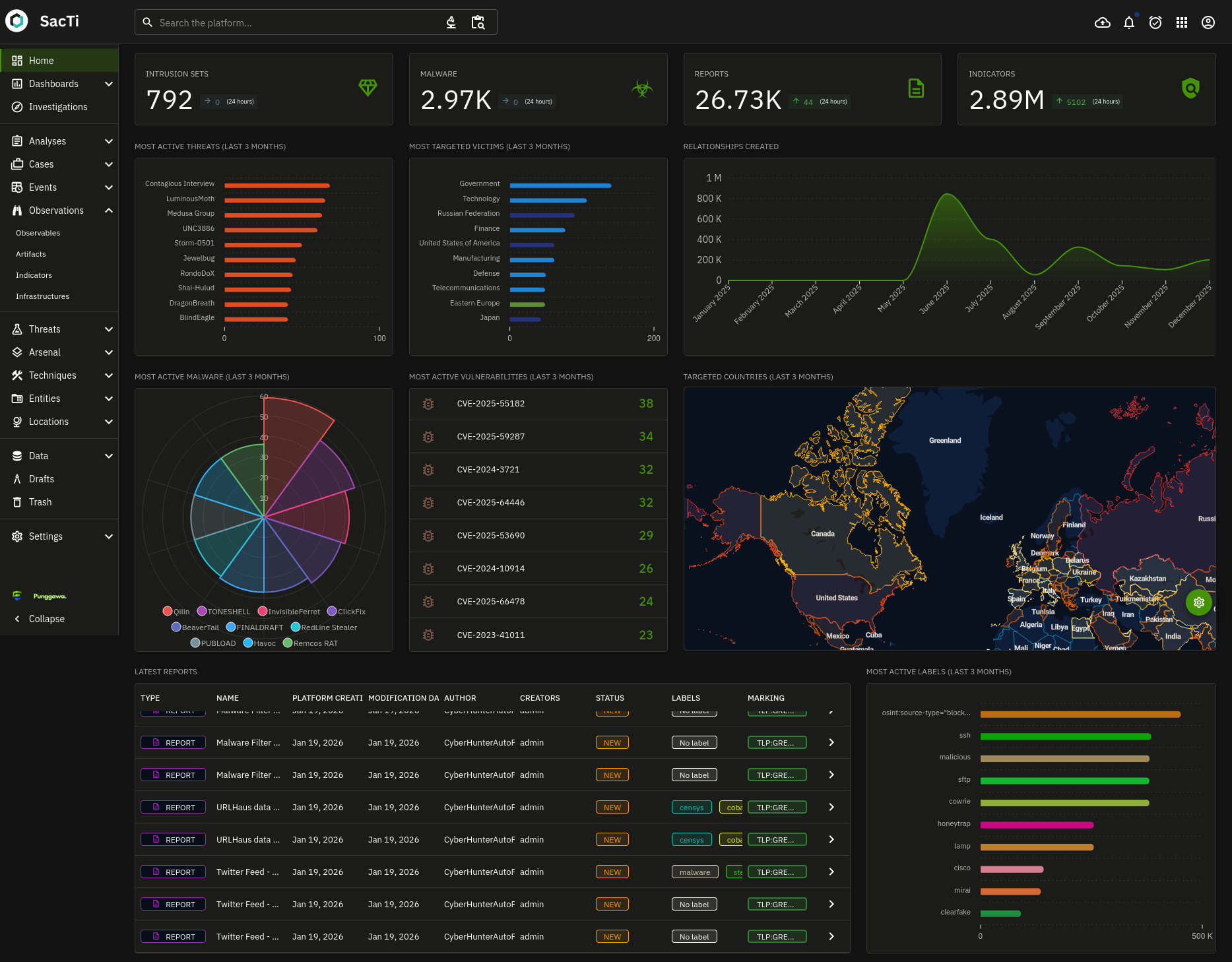
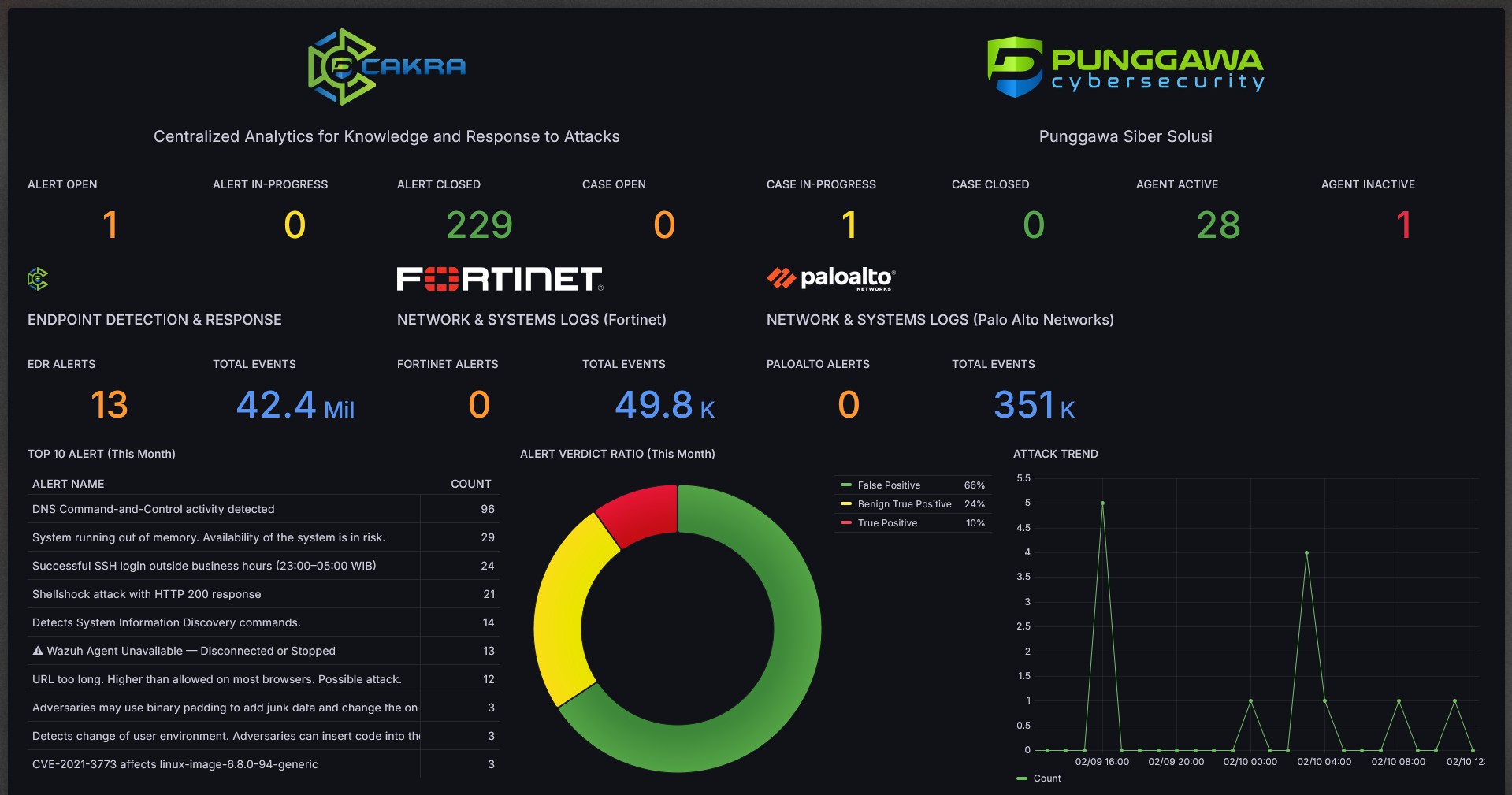
SACTI
Threat Hunting Platform - Proactive detection of advanced and hidden threats
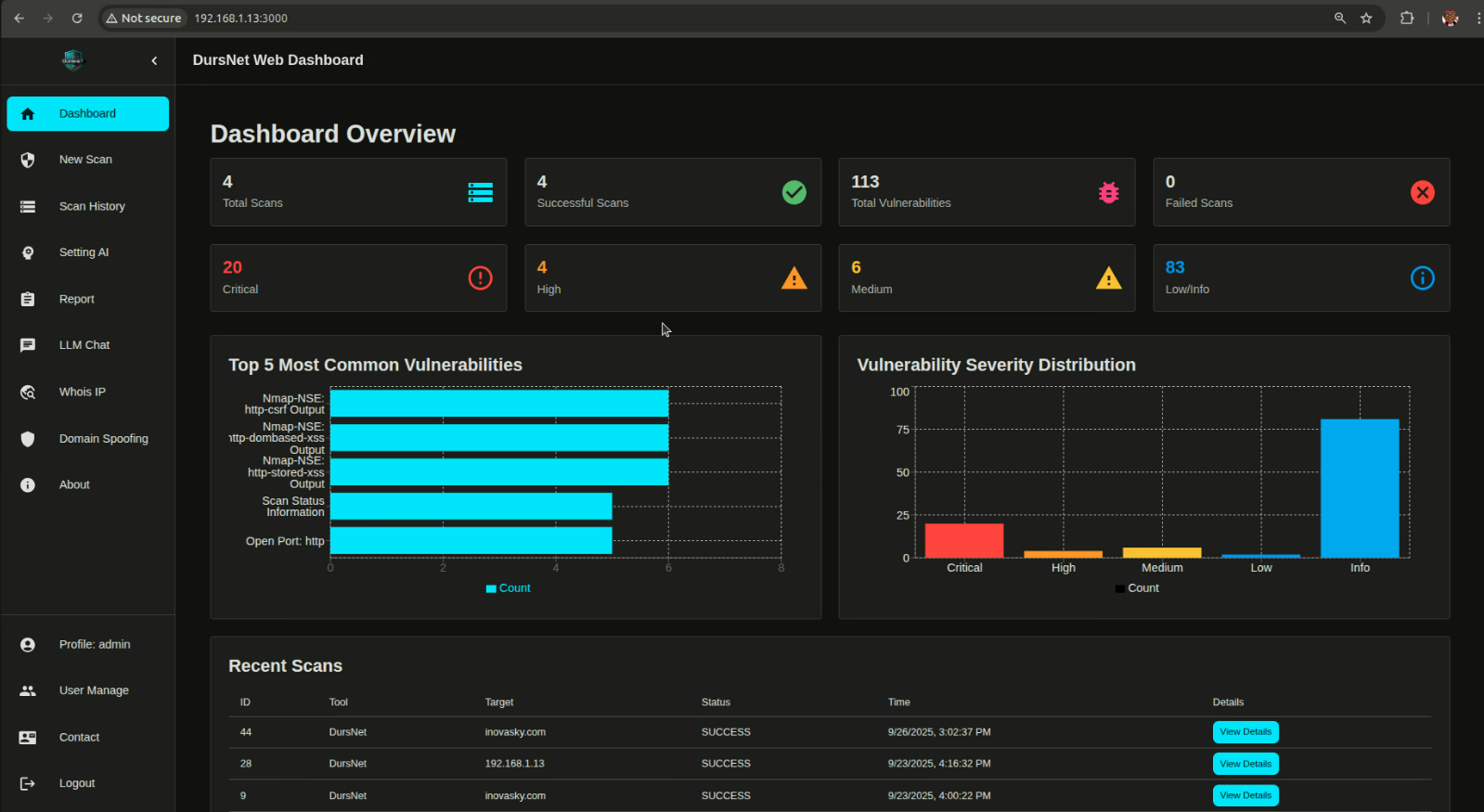
DURSNET
Network Vulnerability Scanner - Discover, assess, and remediate network security
Unified Security Platform
Seamless integration across all security products for comprehensive protection
 SACTI
SACTI
 DURSNET
DURSNET
Why Choose Punggawa Products
Enterprise-grade security built for modern threats
Enterprise-Grade
Built for scale with enterprise security and compliance standards
AI-Assisted
Machine learning powered threat detection and analysis
High Performance
Real-time processing of millions of security events
SOC-Ready
Modern interface designed for security operations teams
CAKRA
Security Information & Event Management (SIEM)
Centralized visibility and real-time security intelligence
Unified Security Intelligence
Our SIEM platform provides centralized visibility across your entire security infrastructure, correlating events from multiple sources to detect threats in real-time.
- Centralized log ingestion from all security tools
- Real-time correlation and alerting engine
- Compliance-ready dashboards and reports
- Scalable architecture for enterprise SOC
Key Capabilities
Log Management
Ingest, normalize, and store logs from any source at scale
Correlation Engine
Advanced threat detection through multi-source correlation
Real-Time Alerts
Instant notifications for critical security events
Compliance Reporting
Pre-built reports for regulatory compliance requirements
Custom Dashboards
Build personalized views for your security operations
SACTI
Threat Hunting & Detection
Discover, assess, and remediate network security risks
Proactive Defense
Go beyond reactive security with analyst-driven threat hunting capabilities. Uncover sophisticated attacks before they cause damage.
- Behavioral and anomaly-based detection
- MITRE ATT&CK framework integration
- Threat intelligence enrichment
- Investigation workflow automation
Key Capabilities
MITRE ATT&CK Hunting
Framework-based threat hunting methodologies
Behavioral Analytics
Machine learning-powered anomaly detection
Threat Intel
Real-time threat intelligence feed integration
Investigation Tools
Advanced forensic and analysis capabilities
DURSNET
Network Vulnerability Scanner
Discover, assess, and remediate network security risks
Comprehensive Risk Assessment
Automated discovery and assessment of your network infrastructure. Identify vulnerabilities and misconfigurations before attackers do.
- Automated asset discovery across your network
- CVE-based vulnerability detection
- Risk scoring and prioritization
- Actionable remediation guidance
Key Capabilities
Network Discovery
Automatic asset and service identification
CVE Scanning
Comprehensive vulnerability database coverage
Risk Prioritization
CVSS-based scoring and remediation prioritization
Remediation Guidance
Step-by-step fix instructions for each finding